A huge intelligence screw-up turned the government and private companies into cyberwarfare partners
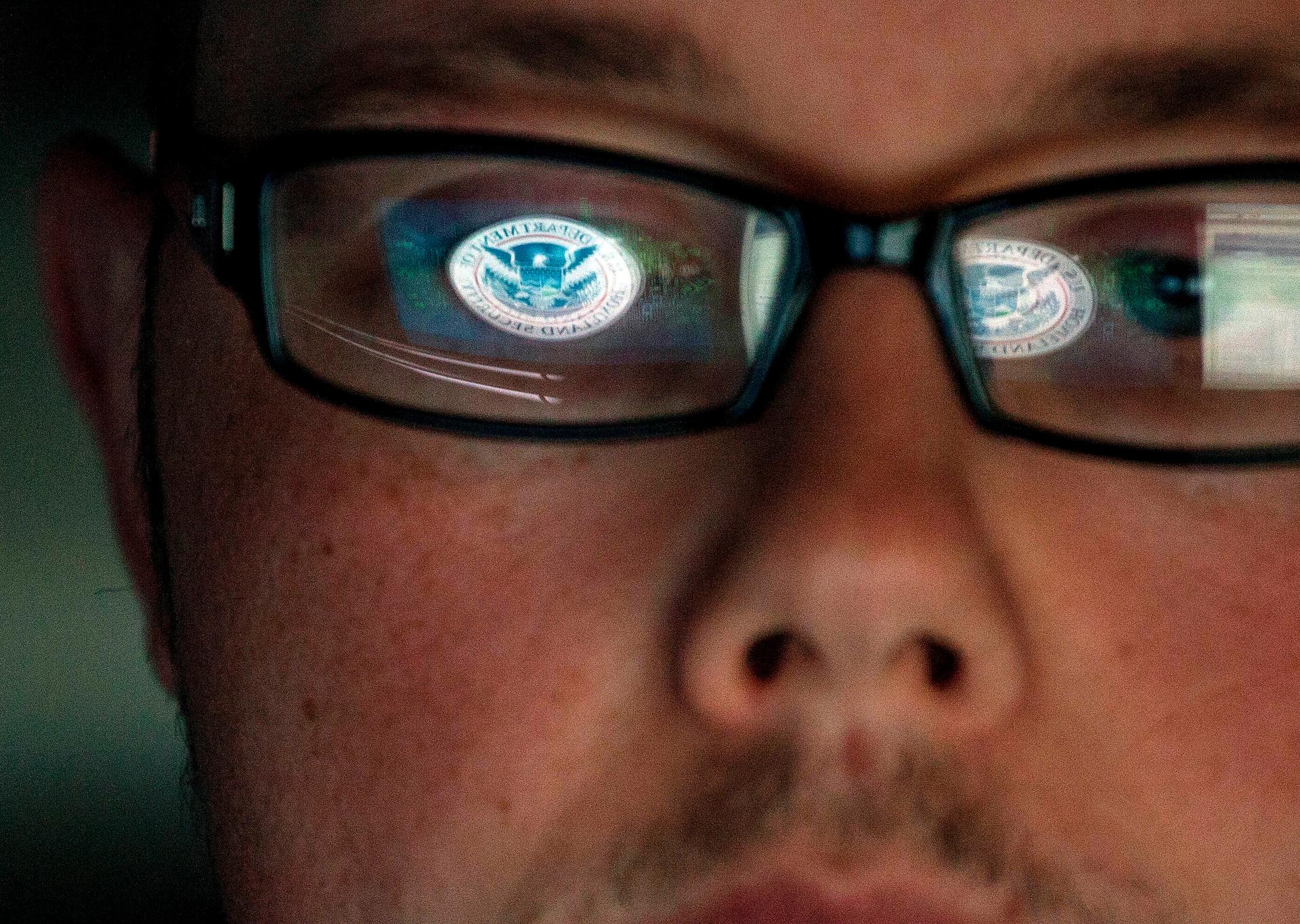
A cyber security analyst works in a watch and warning center at a Department of Homeland Security cyber security defense lab at the Idaho National Laboratory.
The spies had come without warning. They plied their craft silently, stealing secrets from the world’s most powerful military. They were at work for months before anyone noticed their presence. And when American officials finally detected the thieves, they saw that it was too late. The damage was done.
The intruders had made off with huge amounts of technical and design information about the United States’ most important new weapon, a next-generation aircraft called the Joint Strike Fighter. It was supposed to be the fighter to end all fighters, which would be flown by every branch of the armed forces and ensure America’s aerial dominance for decades to come. Dubbed the F-35, the jet was the most complex military weapons system ever devised and, with an estimated total price tag of $337 billion, the most expensive.
All signs pointed to China’s military as the culprit in a series of audacious raids that began in late 2006. It had the motive and the opportunity to steal the F-35’s secrets, particularly details about how the fighter evaded enemy radar systems. For decades China had waged an aggressive espionage campaign against the US Armed Forces, its most formidable adversary. Beginning in the late 1970s, Chinese agents working in or visiting American universities, government research labs, and defense contractors made off with design information about weapons systems, including nuclear warheads.
But there was something strange about the Joint Strike Fighter theft. The spies weren’t taking paper documents out of offices or eavesdropping on engineers in the break room. They were stealing information remotely, via a computer connection. The Joint Strike Fighter program had been hacked.
Computer forensics investigators at the air force, which was in charge of the F-35 program, started looking for the culprits. To understand how the hackers had gotten in, they had to think like them. So they brought in a hacker. He was an ex–military officer and a veteran of the military’s clandestine cyber campaigns. He’d cut his teeth in some of the army’s earliest information-warfare operations in the mid-1990s, the kind designed to get inside an enemy’s head more than his databases. These were computer-age variants of classic propaganda campaigns; they required military hackers to know how to penetrate an enemy’s communications systems and transmit messages that looked as if they came from a trusted source. Later the former officer’s work evolved into going after insurgents and terrorists on the battlefields of Iraq, tracking them down via their cell phones and Internet messages. He was only in his mid-forties, but by the standards of his profession he was an old hand.
This much the air force knew about the Joint Strike Fighter breach: the data hadn’t been taken from a military computer. It seemed to have come from a company that was hired to help design and build the aircraft. The spies had made an end run, targeting Defense Department contractors whose computers were full of highly classified information, including some of the same plans for the F-35 that were likely to be found on a military system. It was a shrewd tactic. Contractors are an indispensable part of the American military; without them, planes don’t fly, tanks don’t roll, and ships aren’t built and repaired. But their computer systems were generally less defended than the military’s top-secret networks, the most sensitive of which weren’t even connected to the Internet. The hackers simply found another way in, targeting the firms to which the military outsourced so many of its key operations.
The air force investigators weren’t sure which company was the source of the breach. It could be Lockheed Martin, the lead contractor on the F-35 program, or its two main subcontractors, Northrop Grumman and BAE Systems, or any one of the more than one thousand other firms and suppliers hired to work on the jet’s many mechanical systems or its elaborate electronics. About 7.5 million lines of software code helped run the aircraft itself — more than three times the number in the service’s current top-of-the-line fighter. Another 15 million lines of code ran the jet’s logistics, training, and other support systems. For a spy, this was what the military would call a “target-rich environment.” Anywhere he looked he might find secrets about the aircraft’s navigation systems, its onboard sensors and surveillance equipment, and its weaponry.
The logical place to start the investigation was with Lockheed Martin, the primary contractor. Its own computers held vital information about the aircraft, but perhaps more important, it was in charge of the many subcontractors to whom various aspects of the F-35’s development had been farmed out. But when the air force’s hacker showed up at a Lockheed office to start his investigation, he was met not by fellow techies or military officers overseeing the F-35’s construction. He was greeted by the company’s lawyers.
The hacker requested a laptop. “Why do you need that?” the lawyers asked. He explained that he had to look at Lockheed’s internal computer networks, for starters. Also, he wanted to know what software and applications a typical Lockheed employee’s laptop was running. They might have flaws in software code or “backdoors,” which allow a user (including a legitimate one, such as a systems administrator) to bypass normal security controls, like a user log-in and password screen, and gain access to the machine. An intruder could have used these access points to gain a foothold inside the company’s electronic infrastructure. All the spy needed was a way in, a place to set up a digital beachhead and conduct operations.
The lawyers gave the hacker a laptop fresh out of the box; it had never been connected to a Lockheed network. It had never been touched by a Lockheed employee — other than an attorney. The hacker protested. This was like being asked to figure out how a house was burgled without being allowed to inspect the crime scene.
Why would Lockheed, which stood to make billions building the Joint Strike Fighter, not do everything it could to help find the spies? Maybe because a thorough investigation might reveal how poorly defended the company’s networks were. Investigators might even find evidence of other breaches, on other military programs. Word that it had been infiltrated by spies who’d never set foot on company property could hardly help its business. Lockheed was the single-largest provider of goods and services to the US government. In 2006 it held at least $33.5 billion in contracts, more than 80 percent of which were with the Defense Department. And those figures don’t include secret work for intelligence agencies, which surely totaled billions more. Lockheed couldn’t afford to be seen as a poor steward of the government’s most precious secrets — indeed, no defense contractor could. Lockheed was also a publicly traded company. Presumably, shareholders would react negatively to news that it couldn’t protect the information at the core of its multibillion-dollar business.
Unsurprisingly, the hacker found nothing useful on the laptop. The top air force generals charged with seeing the Joint Strike Fighter to completion were furious about the breach, and they demanded that Lockheed, and all the other contractors involved, cooperate fully with the investigation. As they saw it, these companies didn’t just work for the government. They were effectively part of the government, sustained by taxpayer dollars and entrusted with top-secret work. The air force expanded its investigation, and over the next several months the hacker and his colleagues scrutinized Lockheed’s networks and those of other contractors working on the program.
The investigators discovered that this was no one-off break-in. Lockheed’s networks had been breached repeatedly. They couldn’t say precisely how many times, but they judged the damage as severe, given the amount of information stolen and the intruders’ unfettered access to the networks. In the entire campaign, which also targeted other companies, the spies had made off with several terabytes of information on the jet’s inner workings. In absolute size, that was roughly equal to 2 percent of the collection of the Library of Congress.
In another era, running a human spy inside an American corporation and planting a listening device would have counted as a heroic feat of espionage. Now one just had to infect a computer with a malicious software program or intercept a communication over the Internet and listen in from the other side of the world.
The more investigators combed Internet logs and computer drives, the more victims they found. The spies had penetrated the networks of subcontractors in several countries. Technicians traced the Internet protocol addresses and the techniques the spies had used. There was little doubt they were in China, and were probably the same group that has been linked to other break-ins aimed at the US military and large American companies, particularly in the technology and energy industries. The breadth, persistence, and sophistication of Chinese cyber espionage was just beginning to dawn on US military and intelligence leaders. Whether they feared embarrassment and ridicule or because they didn’t want to tip off the Chinese that they were being watched, US officials didn’t publicly reveal the extent of the espionage.
The spies were hunting for details about the fighter’s mechanical design and how well it held up under the stresses of flight and aerial combat. This suggested that they wanted to learn the weaknesses of the aircraft — but also that they wanted to build one themselves. The implications were chilling. Presuming the spies were working for the Chinese military, American fighters might one day go into battle against their clones. American pilots might be flying against Chinese foes who already knew the F-35’s vulnerabilities.
At the moment, the jet’s sensors and flight controls, which allowed the aircraft to detect its adversaries or perform complicated maneuvers, appeared to be safe, because those plans were stored on computers that weren’t connected to the Internet. But more than a year later, investigators were still discovering breaches that they’d missed earlier. One had to assume that the campaign might continue, and that even an offline computer was a target. The very fact that it wasn’t connected to the public network suggested it contained the most sensitive information.
Investigators eventually concluded that the spies weren’t initially looking for information about the F-35 at all but that they’d targeted another classified program. Perhaps they found it an easier target given how much information was lying unprotected on company networks. That they’d switched plans mid-heist hinted at the spies’ audacity. Some officials marveled at how little care the intruders took to cover themselves. They didn’t seem to care if they were exposed. It was like they were daring the Americans to come after them, believing they wouldn’t.
Excerpted from "@WAR: The Rise of the Military-Internet Complex" by Shane Harris. Copyright © 2014 by Shane Harris. Used by permission of Eamon Dolan Books / Houghton Mifflin Harcourt Publishing Company. All rights reserved.